Fog Ransomware Group Exposed: Inside the Tools, Tactics, and Victims of a Stealthy Threat
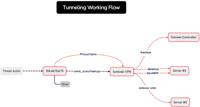
Image: DFIR Report’s Threat Intel Group
In a new investigation, The DFIR Report’s Threat Intel Group has shed light on the growing operations of the Fog ransomware group, revealing a sophisticated ars …
Read more
Published Date:
Apr 29, 2025 (2 hours, 55 minutes ago)
Vulnerabilities has been mentioned in this article.
Source: Read More

