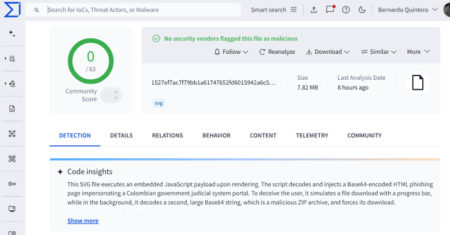
The threat actor behind the malware-as-a-service (MaaS) framework and loader called CastleLoader has also developed a remote access trojan known as CastleRAT.
“Available in both Python and C variants, CastleRAT’s core functionality consists of collecting system information, downloading and executing additional payloads, and executing commands via CMD and PowerShell,” Recorded Future Insikt Group
Source: Read More