A phishing campaign is bypassing FIDO key authentication by exploiting cross-device sign-in features, a managed detection and response (MDR) provider has discovered.
The attack campaign, reported by Expel, doesn’t involve any vulnerabilities in FIDO keys, but rather exploits the cross-device sign-in functionality developed for user convenience that allows them to sign in on a device that doesn’t have a passkey by using a second device that does.
FIDO Key Attack Starts with Phishing Email
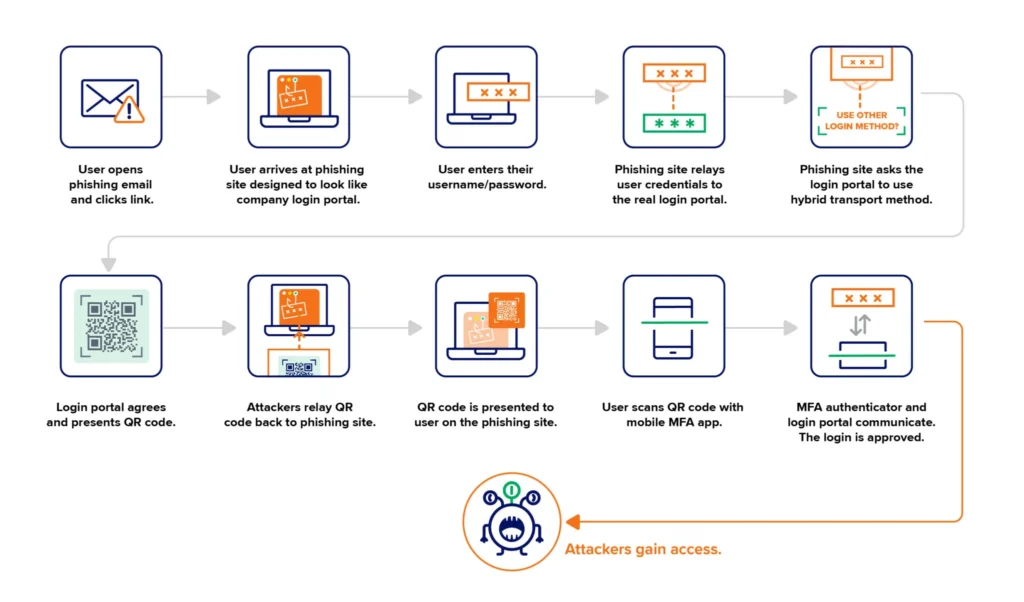
The attack started with a phishing email sent to employees at an Expel customer that attempted to direct them to a fake login page. A user was tricked onto entering their user name and password into the site, then was presented with a QR code.
“What happened behind the scenes is the phishing site automatically sent the stolen username and password to the legitimate login portal of the organization, along with a request to utilize the cross-device sign-in feature of FIDO keys,” the Expel blog said.
The login portal then displayed a QR code, which the phishing site captured and relayed back to the user on the fake site. “The user scans it with their MFA authenticator, the login portal and the MFA authenticator communicate, and the attackers are in,” the blog said.
That process effectively bypassed the FIDO key protections. There was no evidence of further malicious activity in the attack, which was attributed to the PoisonSeed crypto phishing attack group, but Expel said it’s not the only recent case its security operations center (SOC) has seen of threat actors attempting to abuse FIDO keys.
In another case, which likely started with a phishing email, an attacker “reset the user’s password and then enrolled their own FIDO key within the account.”
Protecting FIDO Keys from Attack
FIDO keys “are still a worthwhile investment when it comes to securing accounts,” the authors said, but the rise in attacks targeting FIDO keys gives security teams one more potential threat to monitor – along with some possible controls to better secure FIDO keys.
Possible controls include limiting the geographic locations that users are allowed to log in from, and establishing a registration process for when users travel to different areas.
Monitoring for registration of unexpected keys or unexpected key brands, multiple keys for one user, and keys registered in quick succession are other signs of potential malicious activity.
The researchers also recommended one additional security feature for cross-device sign-in – requiring Bluetooth communication between a mobile device with an MFA authenticator and an unregistered device a user wants to log into.
“This effectively means the user has to be at the system that’s logging into the portal when they scan the QR code,” the blog said. “Enabling this feature will reduce the chances that attackers can use this AitM phishing attack to almost zero.”
Source: Read More