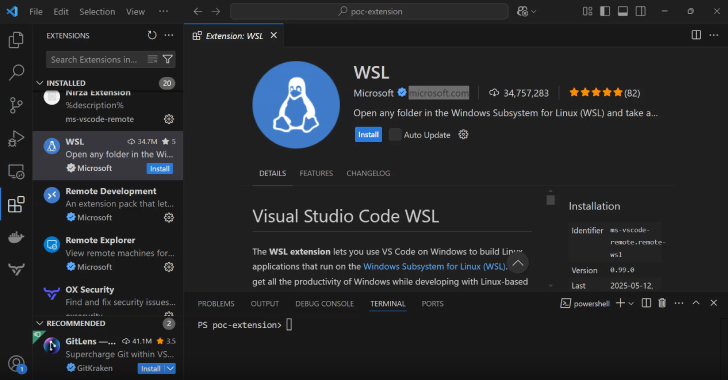
A new study of integrated development environments (IDEs) like Microsoft Visual Studio Code, Visual Studio, IntelliJ IDEA, and Cursor has revealed weaknesses in how they handle the extension verification process, ultimately enabling attackers to execute malicious code on developer machines.
“We discovered that flawed verification checks in Visual Studio Code allow publishers to add functionality
Source: Read More