SafePay’s journey to the top of the ransomware leaderboard was a quick one.
The SafePay ransomware group first emerged in the fall of 2024, and last month took the top spot among ransomware groups in the number of victims claimed on their data leak site, according to a Cyble blog post published today.
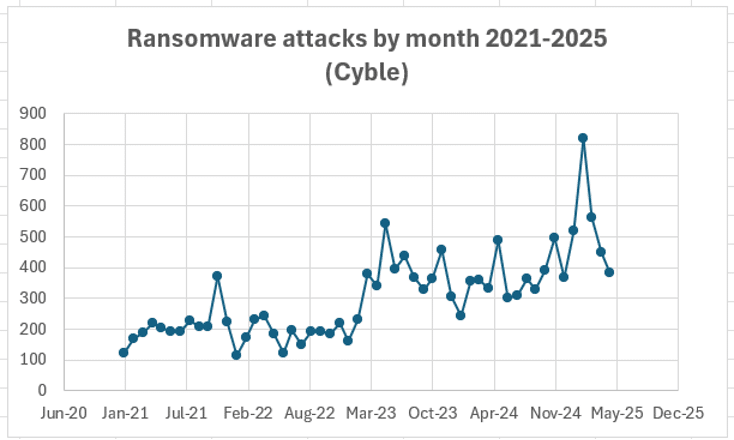
Cyble reported that ransomware groups claimed 384 victims in May, a number that may rise somewhat as all data is processed. That’s the third straight monthly decline for claimed victims, as new leaders continue to emerge after RansomHub – the top ransomware group for more than a year – went offline in late March in a possible attack by rival DragonForce.
Cyble also looked at DevMan, another emerging ransomware threat, and other ransomware developments that occurred in May.
Top Ransomware Groups and Threats
SafePay claimed 58 victims in May to take over the top spot from April leader Qilin, which came in second with 54 victims. Play, Akira and NightSpire rounded out the top five ransomware groups. The U.S. was once again the most targeted country, with 181 victims (charts below from Cyble).


Professional Services and Construction were the most attacked sectors by all ransomware groups, totaling 101 attacks, followed by Manufacturing, Government, Healthcare, Finance, IT, Transportation, Consumer Goods and Education, Cyble said.
SafePay has claimed 198 victims to date. The group’s previous monthly high was 43 victims in March, but May was the first month that SafePay led all ransomware groups.
Cyble said SafePay typically obtains initial access to victim environments through VPN and RDP connections, often using stolen credentials or password spraying attacks. The group uses double-extortion techniques – encrypting and threatening to publicly release data – and claims not to offer Ransomware-as-a-Service (RaaS), unlike other ransomware groups that rely on affiliates to spread their malware.
Major targets for SafePay include the U.S. and Germany, as well as the Professional Services, Construction, Healthcare, Education and Manufacturing sectors.
DevMan, meanwhile, mainly operates as an affiliate of several RaaS groups, but was recently observed deploying its own ransomware that the group claims is capable of faster lateral movement and is implemented via Group Policy Object (GPO). DevMan claimed 13 victims in May, placing it just outside the top five ransomware groups, “and making it one to watch,” Cyble said.
As an affiliate, DevMan has worked with Qilin, Apos, DragonForce RaaS and RansomHub.
In another significant ransomware development in May, the leak of the VanHelsing Ransomware-as-a-Service (RaaS) source code raises “concerns of potential copycat operations, as observed following the leaks of LockBit and Babuk,” Cyble said. “The widespread availability of VanHelsing’s source code may accelerate the emergence of new ransomware variants in the coming weeks.”
Cyble also detailed three new ransomware groups, as well as 17 ransomware attacks claimed by ransomware groups, many of which could have significant impact on the software supply chain, critical infrastructure and even military targets.
Protecting Against Ransomware
Cyble said the rise of new ransomware groups to take the place of former leaders “underscores the ever-present threat of ransomware and highlights the enduring importance of cybersecurity best practices for protecting against a wide range of cyber threats.”
Those cybersecurity best practices include a risk-based vulnerability management program; protecting exposed assets; segmenting networks and critical assets; creating ransomware-resistant backups; applying Zero Trust principles; practicing proper configuration and secrets protection; hardening endpoints and infrastructure; and monitoring networks, endpoints and cloud environments.
Source: Read More