Dutch intelligence officials and Microsoft warned today of a new Russian threat actor targeting Western organizations in what appears to be a military and high-tech espionage campaign.
The new threat group – called Laundry Bear by the Dutch and Void Blizzard by Microsoft – was the subject of separate advisories today. The Netherlands General Intelligence and Security Service (AIVD) and the Netherlands Defense Intelligence and Security Service (MIVD) published a joint advisory, while Microsoft published a separate blog on the group.
The threat group typically targets Microsoft email environments with attack techniques like stolen cookies and password spraying, then expands its attack from there while remaining difficult to detect.
Military and High-Tech Espionage is Laundry Bear Objective
In the Dutch advisory, the agencies said that Laundry Bear/Void Blizzard “has successfully gained access to sensitive information from a large number of government organisations, commercial entities and other organisations around the world, with a specific interest in European Union and NATO member states.”
The threat group largely targets cloud-based email environments, in particular Exchange servers, engaging in “large-scale theft of email messages and other information relating to an organisation’s email contacts, such as a Global Address List (GAL),” the Dutch advisory said. In some cases the group has also managed to obtain files, including data stored on cloud servers.
In 2024, Laundry Bear attacked defense contractors, aerospace firms and other high-tech businesses involved in military production, with the likely goal of obtaining “sensitive information relating to the procurement and production of military goods by Western governments, and weapons deliveries to Ukraine from Western countries,” the Dutch advisory said. The group appears “to have some degree of knowledge about the production and delivery of military goods and the corresponding dependencies.”
Laundry Bear has also attacked businesses “producing advanced technologies which are difficult for Russia to obtain due to Western sanctions,” the advisory said. Civilian organizations and businesses have also been targeted, typically in the IT and high tech sectors, including digital service providers to enterprise customers and government organizations, and some critical sectors.
“Compared to some other Russian threat actors under investigation by the services, LAUNDRY BEAR has a high success rate,” the Dutch advisory said.
Laundry Bear/Void Blizzard Attack Techniques
The Dutch report detailed attack techniques such as pass-the-cookie attacks (likely stolen by infostealer malware and bought by Laundry Bear on a criminal marketplace) and password spraying.
After obtaining access to an account, the group “is capable of stealing email messages from compromised systems at scale. In some cases, the Dutch services have established that LAUNDRY BEAR has stolen data from compromised SharePoint environments, where the group exploits known vulnerabilities to collect login credentials for later operations.”
Because the group restricts its actions to existing access to Microsoft accounts without attempting to expand its access to underlying networks or systems, “it appears to have flown under the radar of network and system administrators relatively easily and for an extended period,” the advisory said.
The Dutch advisory noted similarities between Laundry Bear and the APT28 Russian state-sponsored threat actor, but said the groups “are two distinct threat actors.”
Microsoft Details NGO Campaign
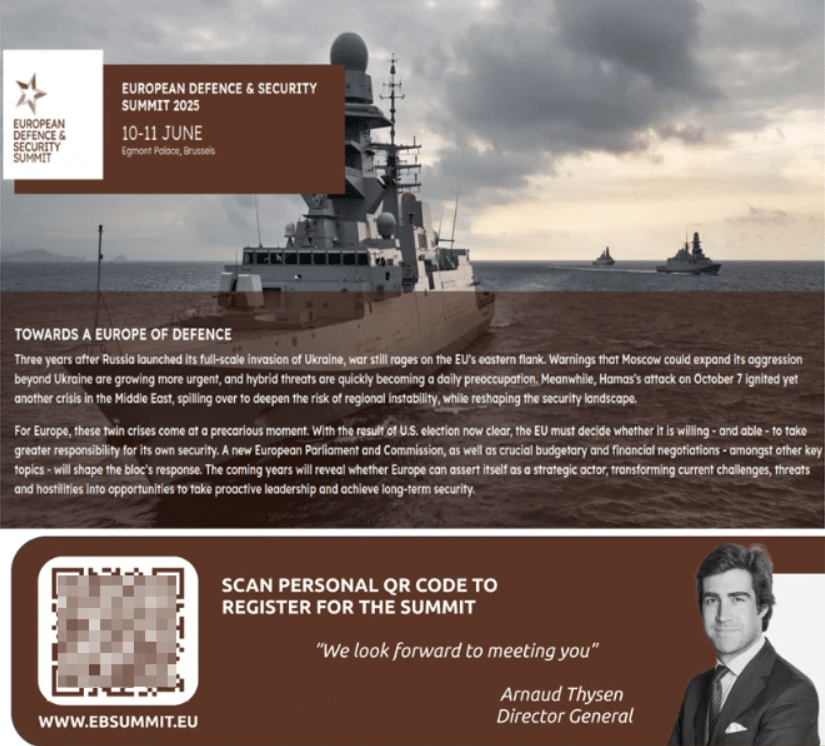
Microsoft detailed an April 2025 adversary-in-the-middle (AitM) spear phishing campaign that targeted more than 20 non-governmental organizations (NGOs) in Europe and the U.S. The group used a typosquatted domain to spoof the Microsoft Entra authentication portal in emails with a PDF attachment that lured targets with a fake invitation to the European Defense and Security Summit.
“The attachment contained a malicious QR code that redirected to Void Blizzard infrastructure micsrosoftonline[.]com, which hosts a credential phishing page spoofing the Microsoft Entra authentication page,” Microsoft said. “We assess that Void Blizzard is using the open-source attack framework Evilginx to conduct the AitM phishing campaign and steal authentication data, including the input username and password and any cookies generated by the server.”
Microsoft has also observed the threat actor accessing Microsoft Teams conversations and messages via the Teams web client application. The threat actor has also enumerated a compromised organization’s Microsoft Entra ID configuration using the publicly available AzureHound tool to gain information about the tenant’s users, roles, groups, applications, and devices.
Protecting Against Laundry Bear/Void Blizzard
The Dutch and Microsoft advisories contain extensive guidance for protecting against the threat group, including implementing automated responses to risky sign-ins, multi-factor authentication, centralized identity management with single sign-on, zero trust principles, cookie expiration and rebinding, and auditing and anomaly detection.
Source: Read More