The U.S. Department of Justice (DOJ) announced that it had obtained and acted on the two court-approved warrants authorizing the seizure of five internet domains linked to a global malware operation known as LummaC2.
The domains were being used by cybercriminals to spread information-stealing malware and were taken down in a coordinated effort involving the DOJ, the FBI, and Microsoft.
Malware has become one of the most common tools in a cybercriminal’s arsenal, offering relatively easy deployment with high impact. Experts often stress that malware attacks not only target large corporations or government agencies but also regular individuals whose personal information can be monetized or used in further attacks.
What is LummaC2 Malware?
LummaC2 malware is a type of information-stealing malware or “infostealer” that has gained notoriety in cybercriminal circles for its effectiveness in targeting and stealing personal and financial data from millions of users worldwide. Once installed on a victim’s device, the malware is capable of harvesting:
Browser history and autofill data
Email and banking login credentials
Cryptocurrency wallet seed phrases
Other sensitive personal information
These stolen details can then be used for various malicious purposes, including unauthorized bank transfers, identity theft, and cryptocurrency fraud.
How the Operation Worked
According to court documents, the administrators of LummaC2 operated the malware through a set of internet domains that served as login portals—referred to as user panels—for authorized users, typically affiliates or cybercriminals who had purchased or leased access to the malware. These portals allowed them to deploy the malware across networks and extract stolen data.
The FBI’s investigation revealed at least 1.7 million instances where LummaC2 was used to compromise victim systems and steal data.

Domain Seizure Details
The Justice Department’s operation unfolded over several days in May 2025:
May 19, 2025: The government seized two domains linked to the LummaC2 infrastructure.
May 20, 2025: In response, LummaC2 administrators notified their users about three newly created domains to restore access to the malware service.
May 21, 2025: The U.S. government swiftly seized the additional three domains, effectively cutting off cybercriminal access to the service again.
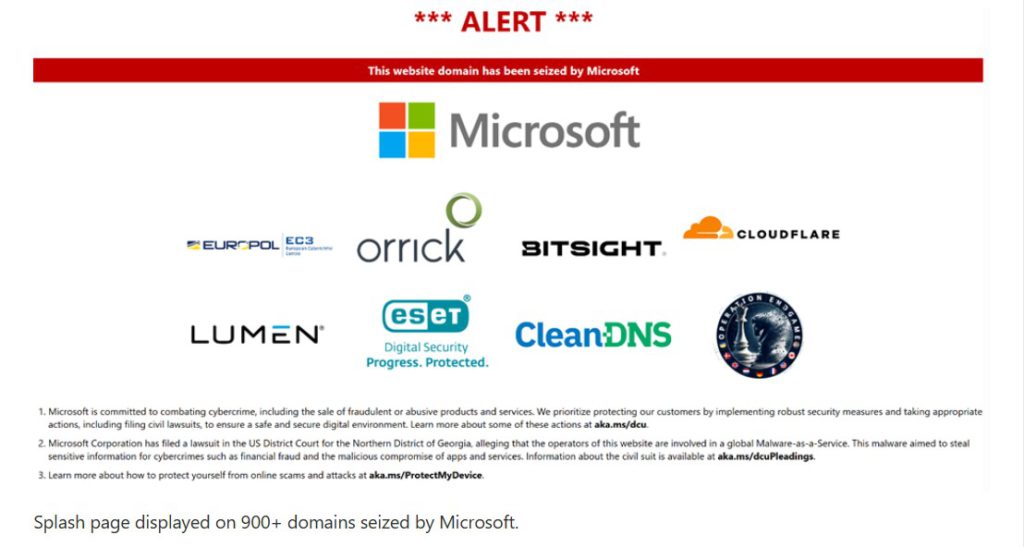
Now, anyone attempting to access these domains is greeted with a notice indicating that the websites have been seized by the Department of Justice and the FBI.

Statements from Officials
Sue J. Bai, head of the DOJ’s National Security Division, emphasized the importance of public-private collaboration in tackling cyber threats:
“Today’s disruption is another instance where our prosecutors, agents, and private sector partners came together to protect us from the persistent cybersecurity threats targeting our country.”
Matthew R. Galeotti, head of the DOJ’s Criminal Division, highlighted the dangers posed by malware like LummaC2:
“This type of malware is used to steal personal data from millions, facilitating crimes such as fraudulent bank transfers and cryptocurrency theft.”
FBI Assistant Director Bryan Vorndran added:
“We took action against the most popular infostealer service available in online criminal markets. Thanks to partnerships with the private sector, we were able to disrupt the LummaC2 infrastructure and seize user panels.”
In a coordinated effort, Microsoft independently launched a civil legal action to take down 2,300 additional internet domains believed to be linked to LummaC2 actors or their proxies. This move reflects a broader public-private initiative to clamp down on cybercrime infrastructure and prevent future attacks.
The operation was led by the FBI’s Dallas Field Office and supported by several branches of the DOJ:
The U.S. Attorney’s Office for the Northern District of Texas
The National Security Division’s National Security Cyber Section
The Criminal Division’s Computer Crime and Intellectual Property Section (CCIPS)
The crackdown on LummaC2 is part of a larger effort by the U.S. government to counter foreign cyber threats. The U.S. Department of State’s Rewards for Justice (RFJ) program is offering up to $10 million for information leading to the identification or location of individuals engaged in malicious cyber activities against U.S. critical infrastructure.

Conclusion
The success of this operation demonstrates the importance of timely coordination between government agencies and private companies like Microsoft.
While the takedown of LummaC2’s infrastructure is a major step forward, one needs to be cautious that similar threats will continue to emerge. Individuals and organizations alike are advised to remain vigilant, adopt strong cybersecurity practices, and stay informed about the latest developments in cybercrime and data protection.
Source: Read More