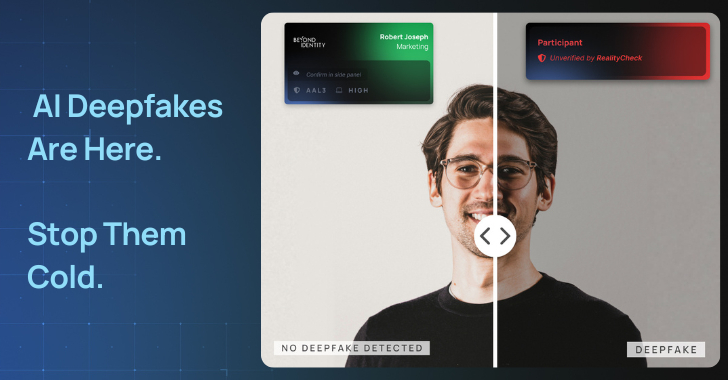
The cybersecurity landscape has been dramatically reshaped by the advent of generative AI. Attackers now leverage large language models (LLMs) to impersonate trusted individuals and automate these social engineering tactics at scale.
Let’s review the status of these rising attacks, what’s fueling them, and how to actually prevent, not detect, them.
The Most Powerful Person on the
Source: Read More