Australian organizations using Fortinet products are being urged to take immediate action following a new advisory highlighting the active exploitation of previously known vulnerabilities. The Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC) has issued this alert primarily for technical users within organizations across the private and public sectors.
Fortinet has observed malicious actors exploiting older, unpatched vulnerabilities to gain and maintain unauthorized access to Fortinet devices. While patches were released previously, many compromised devices were either not updated in time or were attacked before security fixes were applied.
What Happened?
Fortinet’s latest findings reveal a threat actor is actively targeting three known vulnerabilities:
- FG-IR-24-015: Out-of-bounds write vulnerability in sslvpnd.
- FG-IR-23-097: Heap buffer overflow during SSL VPN pre-authentication.
- FG-IR-22-398: Heap-based buffer overflow in sslvpnd.
These issues affect the SSL VPN component in Fortinet’s FortiGate devices, which are commonly used by businesses for secure remote access.
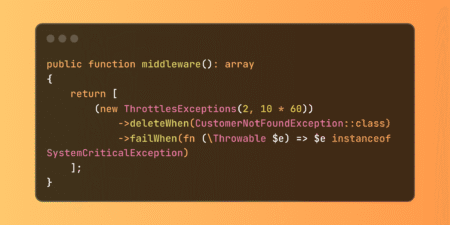
Although Fortinet previously released patches addressing these vulnerabilities, a new technique has been revealed where attackers can retain read-only access to devices even after the original security holes have been patched. This access is achieved by inserting a symbolic link that connects the user and root filesystems through a folder used for serving language files in the SSL VPN.
The symbolic link avoids detection and allows the attacker to read potentially sensitive information such as device configurations.
Importantly, devices without SSL VPN enabled are not affected.
Who Is Affected?
- Organizations that have not updated their Fortinet devices to the latest versions.
- Devices that were compromised before patching may still be at risk due to remnants of the attacker’s access method.
- This threat is not region or industry-specific, and all sectors are encouraged to assess their environments.
How Was It Discovered?
Fortinet’s investigation—supported by internal monitoring and collaboration with third-party organizations—uncovered this post-exploitation technique. The discovery triggered the company’s Product Security Incident Response Team (PSIRT) to develop countermeasures and notify impacted customers.
This new approach by the attacker is a reminder that known vulnerabilities, especially when unpatched, remain an attractive target. Fortinet emphasized that state-sponsored and financially motivated threat actors continue to scan and exploit such vulnerabilities within days of their public disclosure.
What Should You Do Now?
The ASD’s ACSC strongly recommends the following:
- Upgrade all Fortinet devices immediately to one of the following secure versions:
- FortiOS 7.6.2, 7.4.7, 7.2.11, 7.0.17, or 6.4.16
- Review all configurations on affected devices for signs of modification or compromise.
- Investigate your environment for any suspicious behaviour or anomalies in device logs.
What Has Fortinet Done?
To help customers secure their environments and prevent further abuse of these vulnerabilities, Fortinet has taken multiple steps:
- Released updated AV/IPS signatures to detect and remove the symbolic link.
- Enhanced FortiOS versions to:
- Detect and remove the symbolic link during updates.
- Prevent SSL VPNs from serving malicious files.
- Provided direct communication and assistance to known impacted customers based on internal telemetry.
These mitigations are automatically applied if customers have the AV/IPS engine enabled and licensed.
Enhanced Security in New Releases
Customers upgrading to the latest FortiOS versions will benefit from improved security features, such as:
- Virtual patching for interim protection before applying formal patches.
- Firmware integrity validation at the BIOS level.
- Filesystem integrity monitoring through Integrity Measurement Architecture (IMA).
- Automatic updates, allowing devices to receive critical patches without manual intervention.
- Features like Uninterrupted Cluster Upgrade, Auto-restore configurations, and Scheduled patch upgrades for a smoother upgrade process.
These enhancements are part of Fortinet’s broader commitment to cybersecurity best practices and responsible transparency.
Why This Matters
Fortinet’s alert emphasizes a vital principle in cybersecurity: patching alone is not enough if devices are compromised before the fix is applied. Attackers are becoming more advanced, using stealthy techniques like symbolic links to maintain access under the radar.
The incident also highlights the shared responsibility in cybersecurity:
- Vendors must deliver secure products, disclose vulnerabilities responsibly, and support customers with quick fixes.
- Customers must apply patches promptly and maintain strong cyber hygiene to defend against known and emerging threats.
With more than 40,000 vulnerabilities reported in 2024 alone (as per NIST data), managing security updates has become an essential routine for all IT environments.
Source: Read More