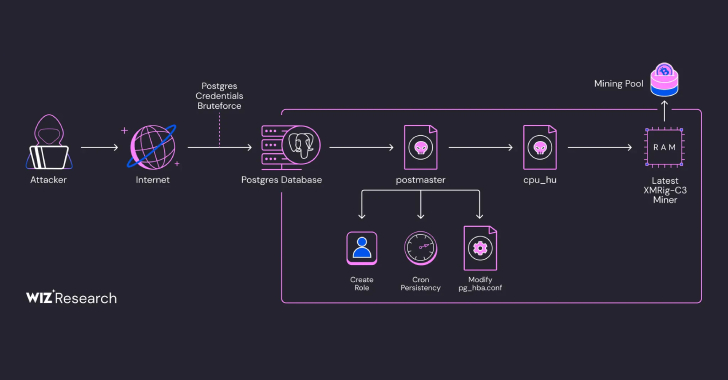
Exposed PostgreSQL instances are the target of an ongoing campaign designed to gain unauthorized access and deploy cryptocurrency miners.
Cloud security firm Wiz said the activity is a variant of an intrusion set that was first flagged by Aqua Security in August 2024 that involved the use of a malware strain dubbed PG_MEM. The campaign has been attributed to a threat actor Wiz tracks as
Source: Read More