The tides have turned in the enterprise AI landscape. According to Menlo Ventures’ 2025 “Mid-Year LLM Market Update,” Anthropic’s Claude…
Development
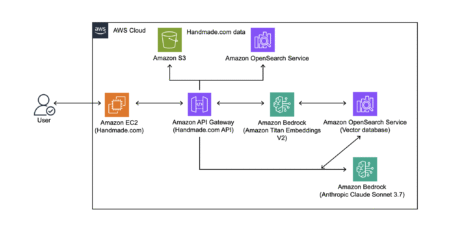
Handmade.com is a leading hand-crafts product marketplace, offering unique, seller-contributed items to customers around the world. With over 60,000 products…
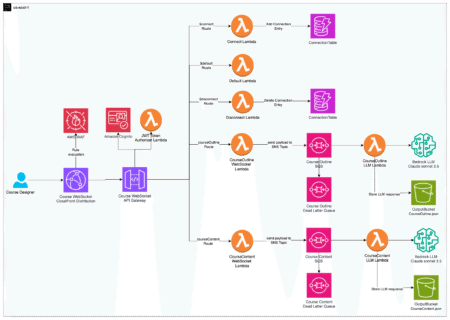
The education sector needs efficient, high-quality course material development that can keep pace with rapidly evolving knowledge domains. Faculty invest…
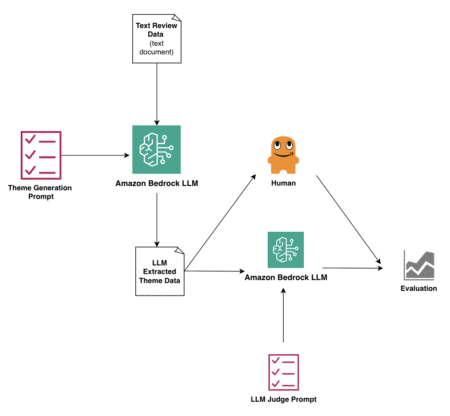
Picture this: Your team just received 10,000 customer feedback responses. The traditional approach? Weeks of manual analysis. But what if…
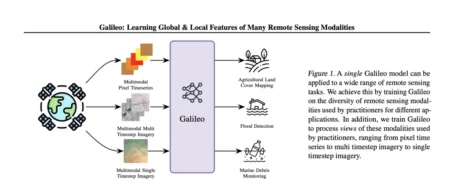
Introduction Galileo is an open-source, highly multimodal foundation model developed to process, analyze, and understand diverse Earth observation (EO) data…
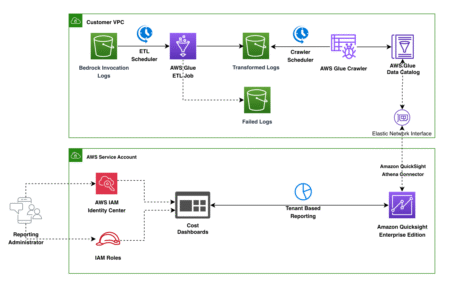
Organizations serving multiple tenants through AI applications face a common challenge: how to track, analyze, and optimize model usage across…
React and Tailwind CSS are popular tools for frontend web development. If you want to become a frontend developer, learning…
Let’s be honest – coding isn’t always easy. Some days, you’re laser-focused, knocking out feature after feature. Other days, you…
Optimizely provides powerful tools that make it easy to build, release, and manage cloud infrastructure efficiently. Optimizely Mission Control Access…
This year marked an exciting milestone in Perficient’s long-standing commitment to automotive innovation as we celebrated the third year of…
A quick overview of all changes and news from the entire Total.js Platform. Read more about our work. Source: Read…
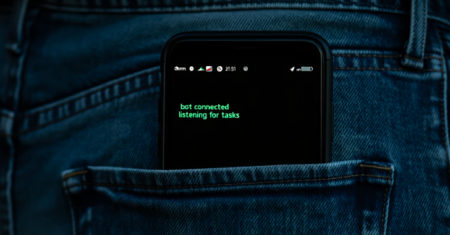
Cybersecurity researchers have discovered a nascent Android remote access trojan (RAT) called PlayPraetor that has infected more than 11,000 devices,…
Everyone’s an IT decision-maker now. The employees in your organization can install a plugin with just one click, and they…
Some of the most devastating cyberattacks don’t rely on brute force, but instead succeed through stealth. These quiet intrusions often…
Malware isn’t just trying to hide anymore—it’s trying to belong. We’re seeing code that talks like us, logs like us,…
Cybersecurity researchers are calling attention to a new wave of campaigns distributing a Python-based information stealer called PXA Stealer. The…
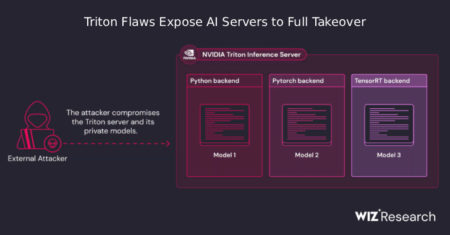
A newly disclosed set of security flaws in NVIDIA’s Triton Inference Server for Windows and Linux, an open-source platform for…
The Shift-Right approach is rapidly becoming a cornerstone of modern quality engineering, offering enterprises a smarter way to ensure software excellence post-deployment. Unlike the traditional Shift-Left model, which focuses on early testing in the development lifecycle, Shift-Right emphasizes continuous validation in production using real-user data and behavior insights. This strategy helps organizations improve customer experience, resolve issues faster, and make data-informed decisions with greater precision. Read the blog now
The post Shift-Right Testing Isn’t Optional Here’s How AI and Real Users Are Making It Work first appeared on TestingXperts.
Please keep in mind, I’m just trying to get points so I can join a particular group. I need 20. But if you feel like you could give a decent answer, I’m all ears.
The code architecture thing being bugless is more of me perusing through stack exchange and seeing so many “How come when I do this this happens” or “when I place this and I’ve been doing it for years. This happens but I can’t do it now with this new thing?”
It seems like a lot of of stuff not working cuz they’re no longer compatible or something’s “flipped” incorrectly or needs to be “connected” to the correct calibrator (I’m sure I’m saying gibberish), but the idea is essentially the same. Why are there so many tiny technical incompatibilities? Isn’t there some form of architecture that just limits this or makes it impossible to happen?
Someone should get on that (I ask ignorantly)
Just curious: I’ve always written tests in a declarative style especially with page object model. But doesn’t this break the single responsibility principle? I used to write things with an imperative style but maintenance was a headache and it was harder to read.
So my question is: Is there a general consensus of which we should be using in our tests? And if it IS declarative, doesn’t that break SOLID (specifically the S) principles?