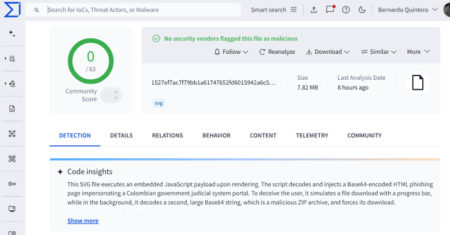
Cybersecurity researchers have flagged a new malware campaign that has leveraged Scalable Vector Graphics (SVG) files as part of phishing…
Development
Chess.com, one of the world’s largest online platforms for playing chess, has disclosed a data breach affecting 4,541 people, including…
Texas Attorney General Ken Paxton has filed a lawsuit against PowerSchool, a California-based education technology provider. Lawsuit is filed over…
Czechia’s national cybersecurity watchdog has issued a warning about foreign cyber operations, focussed on Chinese data transfers and remote administration,…
A critical security vulnerability impacting SAP S/4HANA, an Enterprise Resource Planning (ERP) software, has come under active exploitation in the…
In one of the international enforcement actions, the Alliance for Creativity and Entertainment (ACE), working alongside Egyptian authorities, has shut…
The U.S. Department of Justice has initiated a civil forfeiture action targeting $848,247 in Tether (USDT), suspected to be proceeds…
Parents are being reminded to exercise caution about the toys that they purchase their children, after the United States Federal…
The threat actor behind the malware-as-a-service (MaaS) framework and loader called CastleLoader has also developed a remote access trojan known…
A 30‑year‑old man has been charged with launching a cyberattack on the German subsidiary of Russia’s state-owned oil giant Rosneft.…
Federal Civilian Executive Branch (FCEB) agencies are being advised to update their Sitecore instances by September 25, 2025, following the…
Fine-tuning helps you become a master and professional in AI engineering. We just posted a course on the freeCodeCamp.org YouTube…
Our novel Deep Loop Shaping method improves control of gravitational wave observatories, helping astronomers better understand the dynamics and formation…
3D printing has come a long way since its invention in 1983 by Chuck Hull, who pioneered stereolithography, a technique…
Drupal 11’s AI Features: What They Actually Mean for Your Team If you’ve been following the Drupal community lately, you’ve…
These days, data is pretty much everywhere, and come 2025, it’s more valuable, more regulated, and honestly more complicated than…
Perficient is proud to be included in the IDC Market Glance: Digital Business Professional Services, 3Q25, (Doc # US52789825, July 2025)”.…
A newly disclosed security flaw in the Linux UDisks daemon has been reported. Tracked as CVE-2025-8067, the out-of-bounds read vulnerability…
Google is once again in the crosshairs of French regulators. France’s data watchdog, the CNIL, has fined the tech giant…
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added two security flaws impacting TP-Link wireless routers to its…