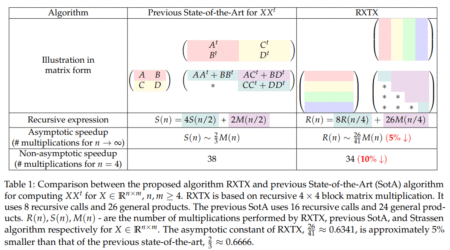
Discovering faster algorithms for matrix multiplication remains a key pursuit in computer science and numerical linear algebra. Since the pioneering…
Development
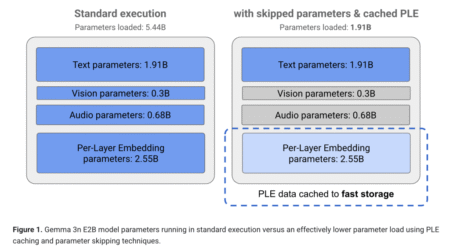
Researchers are reimagining how models operate as demand skyrockets for faster, smarter, and more private AI on phones, tablets, and…
Addressing Architectural Trade-offs in Language Models As language models scale, balancing expressivity, efficiency, and adaptability becomes increasingly challenging. Transformer architectures…
Machine unlearning is a promising approach to mitigate undesirable memorization of training data in ML models. In this post, we…
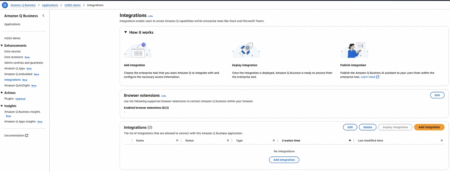
Amazon Q Business, with its enterprise grade security, seamless integration with multiple diverse data sources, and sophisticated natural language understanding,…
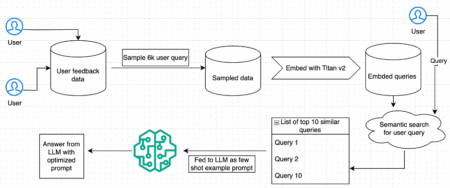
Improving response quality for user queries is essential for AI-driven applications, especially those focusing on user satisfaction. For example, an…
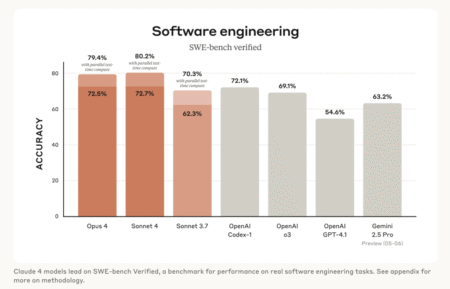
Anthropic has announced the release of its next-generation language models: Claude Opus 4 and Claude Sonnet 4. The update marks…
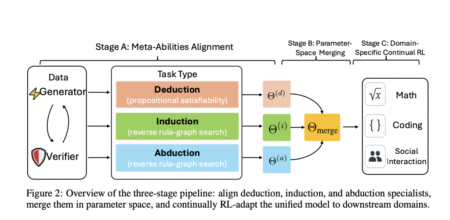
Large Reasoning Models (LRMs) like OpenAI’s o1 and o3, DeepSeek-R1, Grok 3.5, and Gemini 2.5 Pro have shown strong capabilities…
Modern web usage spans many digital interactions, from filling out forms and managing accounts to executing data queries and navigating…
CVE ID : CVE-2025-4642
Published : May 22, 2025, 11:15 p.m. | 1 hour, 35 minutes ago
Description : Rejected reason: This CVE ID has been rejected or withdrawn by its CVE Numbering Authority.
Severity: 0.0 | NA
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-48371
Published : May 22, 2025, 11:15 p.m. | 1 hour, 35 minutes ago
Description : OpenFGA is an authorization/permission engine. OpenFGA versions 1.8.0 through 1.8.12 (corresponding to Helm chart openfga-0.2.16 through openfga-0.2.30 and docker 1.8.0 through 1.8.12) are vulnerable to authorization bypass when certain Check and ListObject calls are executed. Users are affected under four specific conditions: First, calling Check API or ListObjects with an authorization model that has a relationship directly assignable by both type bound public access and userset; second, there are check or list object queries with contextual tuples for the relationship that can be directly assignable by both type bound public access and userset; third, those contextual tuples’s user field is an userset; and finally, type bound public access tuples are not assigned to the relationship. Users should upgrade to version 1.8.13 to receive a patch. The upgrade is backwards compatible.
Severity: 0.0 | NA
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-4338
Published : May 22, 2025, 11:15 p.m. | 1 hour, 35 minutes ago
Description : Lantronix Device installer is vulnerable to XML external entity (XXE) attacks in configuration files read from the network device. An attacker could obtain credentials, access these network devices, and modify their configurations. An attacker may also gain access to the host running the Device Installer software or the password hash of the user running the application.
Severity: 6.8 | MEDIUM
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-4562
Published : May 22, 2025, 11:15 p.m. | 1 hour, 35 minutes ago
Description : Rejected reason: This CVE ID has been rejected or withdrawn by its CVE Numbering Authority.
Severity: 0.0 | NA
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-4692
Published : May 23, 2025, 12:15 a.m. | 35 minutes ago
Description : Actors can use a maliciously crafted JavaScript object notation (JSON) web token (JWT) to perform privilege escalation by submitting the malicious JWT to a vulnerable method exposed on the cloud platform. If the exploit is successful, the user can escalate privileges to access any device managed by the
ABUP Cloud Update Platform.
Severity: 6.8 | MEDIUM
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-48372
Published : May 22, 2025, 9:15 p.m. | 1 hour, 36 minutes ago
Description : Schule is open-source school management system software. The generateOTP() function generates a 4-digit numeric One-Time Password (OTP). Prior to version 1.0.1, even if a secure random number generator is used, the short length and limited range (1000–9999) results in only 9000 possible combinations. This small keyspace makes the OTP highly vulnerable to brute-force attacks, especially in the absence of strong rate-limiting or lockout mechanisms. Version 1.0.1 fixes the issue.
Severity: 0.0 | NA
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-48373
Published : May 22, 2025, 9:15 p.m. | 1 hour, 36 minutes ago
Description : Schule is open-source school management system software. The application relies on client-side JavaScript (index.js) to redirect users to different panels based on their role. Prior to version 1.0.1, this implementation poses a serious security risk because it assumes that the value of data.role is trustworthy on the client side. Attackers can manipulate JavaScript in the browser (e.g., via browser dev tools or intercepting API responses) and set data.role to any arbitrary value (e.g., “admin”), gaining unauthorized access to restricted areas of the application.
Severity: 0.0 | NA
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-48374
Published : May 22, 2025, 9:15 p.m. | 1 hour, 36 minutes ago
Description : zot is ancontainer image/artifact registry based on the Open Container Initiative Distribution Specification. Prior to version 2.1.3 (corresponding to pseudoversion 1.4.4-0.20250522160828-8a99a3ed231f), when using Keycloak as an oidc provider, the clientsecret gets printed into the container stdout logs for an example at container startup. Version 2.1.3 (corresponding to pseudoversion 1.4.4-0.20250522160828-8a99a3ed231f) fixes the issue.
Severity: 0.0 | NA
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-47181
Published : May 22, 2025, 10:15 p.m. | 36 minutes ago
Description : Improper link resolution before file access (‘link following’) in Microsoft Edge (Chromium-based) allows an authorized attacker to elevate privileges locally.
Severity: 8.8 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-4975
Published : May 22, 2025, 10:15 p.m. | 36 minutes ago
Description : When a notification relating to low battery appears for a user with whom the device has been shared, tapping the notification grants full access to the power settings of that device.
Severity: 0.0 | NA
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2024-13953
Published : May 22, 2025, 7:15 p.m. | 1 hour, 30 minutes ago
Description : Sensitive device logger information in ASPECT may be exposed if administrator credentials become compromisedThis issue affects ASPECT-Enterprise: through 3.*; NEXUS Series: through 3.*; MATRIX Series: through 3.*.
Severity: 4.9 | MEDIUM
Visit the link for more details, such as CVSS details, affected products, timeline, and more…