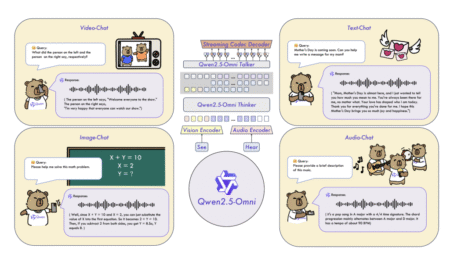
Multimodal foundation models have shown substantial promise in enabling systems that can reason across text, images, audio, and video. However,…
Development
Amazon Bedrock Model Distillation is generally available, and it addresses the fundamental challenge many organizations face when deploying generative AI:…
Critical vulnerability in SAP NetWeaver enables malicious file uploads
Adversaries can exploit CVE-2025-31324 to upload web shells and other unauthorized files to execute on the SAP NetWeaver server April 30, 2025Red Canary has observed activity exploiting a newly-docume …
Read more
Published Date:
Apr 30, 2025 (3 hours, 38 minutes ago)
Vulnerabilities has been mentioned in this article.
CVE-2025-31324
CVE ID : CVE-2025-46557
Published : April 30, 2025, 7:15 p.m. | 3 hours, 53 minutes ago
Description : XWiki is a generic wiki platform. In versions starting from 15.3-rc-1 to before 15.10.14, from 16.0.0-rc-1 to before 16.4.6, and from 16.5.0-rc-1 to before 16.10.0-rc-1, a user who can access pages located in the XWiki space (by default, anyone) can access the page XWiki.Authentication.Administration and (unless an authenticator is set in xwiki.cfg) switch to another installed authenticator. Note that, by default, there is only one authenticator available (Standard XWiki Authenticator). So, if no authenticator extension was installed, it’s not really possible to do anything for an attacker. Also, in most cases, if an SSO authenticator is installed and utilized (like OIDC or LDAP for example), the worst an attacker can do is break authentication by switching back to the standard authenticator (that’s because it’s impossible to login to a user which does not have a stored password, and that’s usually what SSO authenticator produce). This issue has been patched in versions 15.10.14, 16.4.6, and 16.10.0-rc-1.
Severity: 0.0 | NA
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2024-13943
Published : April 30, 2025, 8:15 p.m. | 2 hours, 54 minutes ago
Description : Tesla Model S Iris Modem QCMAP_ConnectionManager Improper Input Validation Sandbox Escape Vulnerability. This vulnerability allows local attackers to escape the sandbox on affected affected Tesla Model S vehicles. An attacker must first obtain the ability to execute low-privileged code on the target system in order to exploit this vulnerability.
The specific flaw exists within the QCMAP_ConnectionManager component. An attacker can abuse the service to assign LAN addresses to the WWAN. An attacker can leverage this vulnerability to access network services that were only intended to be exposed to the internal LAN. Was ZDI-CAN-23199.
Severity: 7.8 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2024-6029
Published : April 30, 2025, 8:15 p.m. | 2 hours, 54 minutes ago
Description : Tesla Model S Iris Modem Race Condition Firewall Bypass Vulnerability. This vulnerability allows network-adjacent attackers to bypass the firewall on the Iris modem in affected Tesla Model S vehicles. Authentication is not required to exploit this vulnerability.
The specific flaw exists within the firewall service. The issue results from a failure to obtain the xtables lock. An attacker can leverage this vulnerability to bypass firewall rules. Was ZDI-CAN-23197.
Severity: 5.0 | MEDIUM
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2024-6030
Published : April 30, 2025, 8:15 p.m. | 2 hours, 54 minutes ago
Description : Tesla Model S oFono Unnecessary Privileges Sandbox Escape Vulnerability. This vulnerability allows local attackers to escape the sandbox on affected Tesla Model S vehicles. An attacker must first obtain the ability to execute code within the sandbox on the target system in order to exploit this vulnerability.
The specific flaw exists within the oFono process. The process allows an attacker to modify interfaces. An attacker can leverage this vulnerability to bypass the iptables network sandbox. Was ZDI-CAN-23200.
Severity: 7.0 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2024-6031
Published : April 30, 2025, 8:15 p.m. | 2 hours, 54 minutes ago
Description : Tesla Model S oFono AT Command Heap-based Buffer Overflow Code Execution Vulnerability. This vulnerability allows local attackers to execute arbitrary code on affected Tesla Model S vehicles. An attacker must first obtain the ability to execute code on the target modem in order to exploit this vulnerability.
The specific flaw exists within the parsing of responses from AT commands. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a heap-based buffer. An attacker can leverage this vulnerability to execute code in the context of the device. Was ZDI-CAN-23198.
Severity: 7.8 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2024-6032
Published : April 30, 2025, 8:15 p.m. | 2 hours, 54 minutes ago
Description : Tesla Model S Iris Modem ql_atfwd Command Injection Code Execution Vulnerability. This vulnerability allows local attackers to execute arbitrary code on affected Tesla Model S vehicles. An attacker must first obtain the ability to execute code on the target system in order to exploit this vulnerability.
The specific flaw exists within the ql_atfwd process. The issue results from the lack of proper validation of a user-supplied string before using it to execute a system call. An attacker can leverage this vulnerability to execute code on the target modem in the context of root. Was ZDI-CAN-23201.
Severity: 7.8 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-27611
Published : April 30, 2025, 8:15 p.m. | 2 hours, 54 minutes ago
Description : base-x is a base encoder and decoder of any given alphabet using bitcoin style leading zero compression. Versions 4.0.0, 5.0.0, and all prior to 3.0.11, are vulnerable to attackers potentially deceiving users into sending funds to an unintended address. This issue has been patched in versions 3.0.11, 4.0.1, and 5.0.1.
Severity: 0.0 | NA
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-2082
Published : April 30, 2025, 8:15 p.m. | 2 hours, 54 minutes ago
Description : Tesla Model 3 VCSEC Integer Overflow Remote Code Execution Vulnerability. This vulnerability allows network-adjacent attackers to execute arbitrary code on affected Tesla Model 3 vehicles. Authentication is not required to exploit this vulnerability.
The specific flaw exists within the VCSEC module. By manipulating the certificate response sent from the Tire Pressure Monitoring System (TPMS), an attacker can trigger an integer overflow before writing to memory. An attacker can leverage this vulnerability to execute code in the context of the VCSEC module and send arbitrary messages to the vehicle CAN bus. Was ZDI-CAN-23800.
Severity: 7.5 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-4136
Published : April 30, 2025, 8:15 p.m. | 2 hours, 54 minutes ago
Description : A vulnerability was found in Weitong Mall 1.0.0. It has been classified as critical. This affects an unknown part of the component Sale Endpoint. The manipulation of the argument ID leads to improper authorization. It is possible to initiate the attack remotely. The exploit has been disclosed to the public and may be used.
Severity: 5.4 | MEDIUM
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2022-27562
Published : April 30, 2025, 9:15 p.m. | 1 hour, 53 minutes ago
Description : Unsafe default file type filter policy in HCL Domino Volt allows upload of .html file and execution of unsafe JavaScript in deployed applications.
Severity: 4.6 | MEDIUM
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2022-42449
Published : April 30, 2025, 9:15 p.m. | 1 hour, 53 minutes ago
Description : Unsafe default file type filter policy in HCL Domino Volt allows upload of .html file and execution of unsafe JavaScript in deployed applications
Severity: 4.6 | MEDIUM
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-24132
Published : April 30, 2025, 9:15 p.m. | 1 hour, 53 minutes ago
Description : The issue was addressed with improved memory handling. This issue is fixed in AirPlay audio SDK 2.7.1, AirPlay video SDK 3.6.0.126, CarPlay Communication Plug-in R18.1. An attacker on the local network may cause an unexpected app termination.
Severity: 0.0 | NA
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-30422
Published : April 30, 2025, 9:15 p.m. | 1 hour, 53 minutes ago
Description : A buffer overflow was addressed with improved input validation. This issue is fixed in AirPlay audio SDK 2.7.1, AirPlay video SDK 3.6.0.126, CarPlay Communication Plug-in R18.1. An attacker on the local network may cause an unexpected app termination.
Severity: 0.0 | NA
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-4139
Published : April 30, 2025, 9:15 p.m. | 1 hour, 53 minutes ago
Description : A vulnerability classified as critical was found in Netgear EX6120 1.0.0.68. Affected by this vulnerability is the function fwAcosCgiInbound. The manipulation of the argument host leads to buffer overflow. The attack can be launched remotely. The vendor was contacted early about this disclosure but did not respond in any way.
Severity: 8.8 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2022-42450
Published : April 30, 2025, 10:15 p.m. | 54 minutes ago
Description : Improper sanitization of SVG files in HCL Domino Volt allows client-side script injection in deployed applications.
Severity: 4.6 | MEDIUM
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2023-37517
Published : April 30, 2025, 10:15 p.m. | 54 minutes ago
Description : Missing “no cache” headers in HCL Leap permits sensitive data to be cached.
Severity: 3.2 | LOW
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2023-45721
Published : April 30, 2025, 10:15 p.m. | 54 minutes ago
Description : Insufficient default configuration in HCL Leap
allows anonymous access to directory information.
Severity: 5.3 | MEDIUM
Visit the link for more details, such as CVSS details, affected products, timeline, and more…