The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) sanctioned a North Korean front company and three…
Development
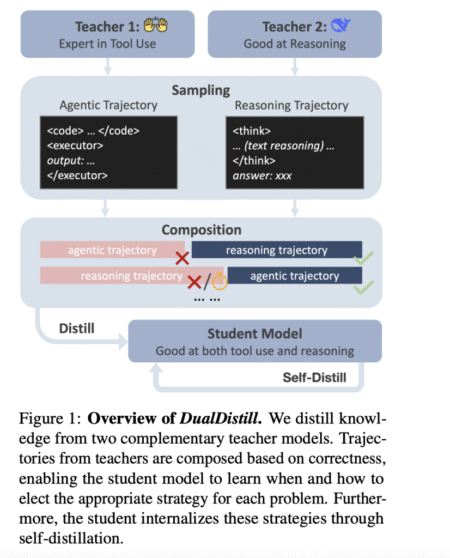
Artificial intelligence research is rapidly evolving beyond pattern recognition and toward systems capable of complex, human-like reasoning. The latest breakthrough…
Existing long-CoT reasoning models have achieved state-of-the-art performance in mathematical reasoning by generating reasoning trajectories with iterative self-verification and refinement.…
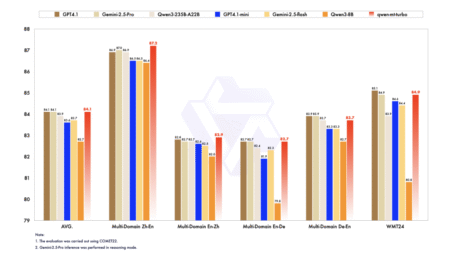
Alibaba has introduced Qwen3-MT (qwen-mt-turbo) via Qwen API, its latest and most advanced machine translation model, designed to break language barriers…
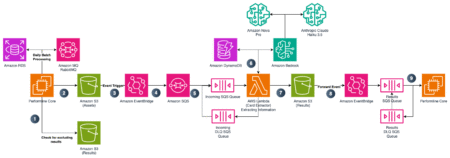
This post is co-written with Bogdan Arsenie and Nick Mattei from PerformLine. PerformLine operates within the marketing compliance industry, a…
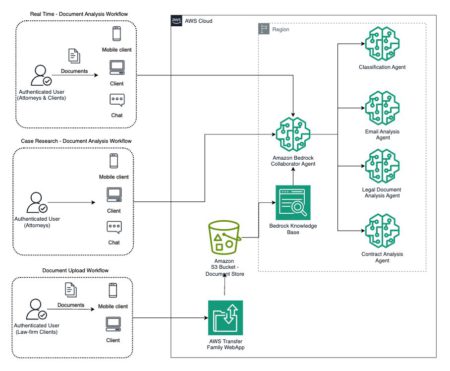
Legal teams spend bulk of their time manually reviewing documents during eDiscovery. This process involves analyzing electronically stored information across…
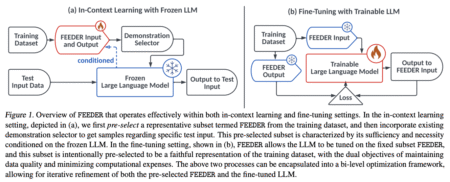
LLMs have demonstrated exceptional performance across multiple tasks by utilizing few-shot inference, also known as in-context learning (ICL). The main…
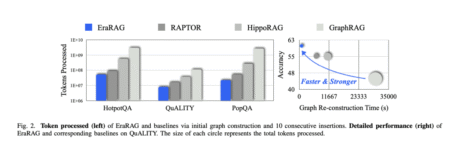
Large Language Models (LLMs) have revolutionized many areas of natural language processing, but they still face critical limitations when dealing…
#746 — July 25, 2025 Read on the Web JavaScript Weekly es-toolkit: A Modern JavaScript Utility Library — Boasts being…
Laravel’s @inject directive enables direct service container access within Blade templates, reducing controller complexity while maintaining clean architecture. Perfect for…
Useful Laravel links to read/watch for this week of July 24, 2025. Source: Read MoreÂ
PHP 8.5 will support recursion in Closures by fetching the currently executing Closure. Learn how you can support recursion using…
Take the State of Laravel 2025 survey to contribute your voice to the Laravel community. By sharing and participating, you…
One of the shared, fundamental goals of most chemistry researchers is the need to predict a molecule’s properties, such as…
City life is often described as “fast-paced.” A new study suggests that’s more true that ever. The research, co-authored by…
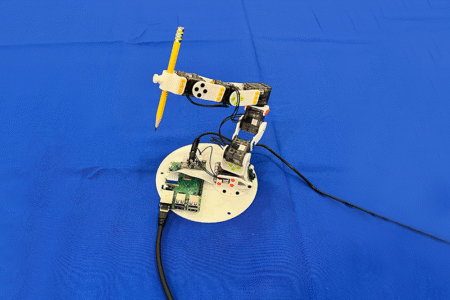
In an office at MIT’s Computer Science and Artificial Intelligence Laboratory (CSAIL), a soft robotic hand carefully curls its fingers…
First, a confession: When I was learning to code, my “workflow” was a mess. Sticky notes. Google Docs. Random Trello…
Discover why design systems are essential for consistent UX in 2025. Learn how top companies like Google, Apple, and IBM…
In the world of software development, speed, scalability, and user experience are paramount. Flutter, with its expressive UI toolkit and…
If you’re building something on your own, you don’t have time to mess around with bloated platforms or complicated setups.…