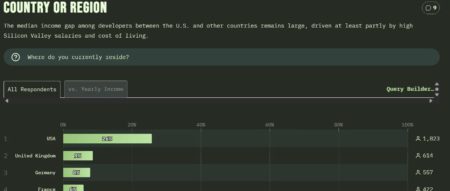
State of Devs 2025 survey results are out! While the survey isn’t directly related to the code part of what we do…
Karere is a native GTK4 application that provides a seamless WhatsApp Web experience integrated with your Linux desktop. The post…
Fastfetch è un’utilità open source pensata per chi desidera un riepilogo chiaro e personalizzabile delle informazioni di sistema direttamente nel…
Estonian deeptech startup Jälle Technologies has secured €2 million Pre-Seed funding to advance its mission of recovering value from end-of-life lithium-ion…
Blender è un potente software di grafica e modellazione 3D, libero, multi-piattaforma e open source. È ampiamente utilizzato per la…
Poweradmin is a friendly web-based DNS administration tool for PowerDNS server. The post Poweradmin – web-based DNS administration tool appeared…
Carlos and Claire found themselves supporting a 3rd party logistics package, called IniFreight. Like most “enterprise” software, it was expensive,…
Cybersecurity researchers have disclosed two security flaws in the Sudo command-line utility for Linux and Unix-like operating systems that could…
MIT researchers have developed a new theoretical framework for studying the mechanisms of treatment interactions. Their approach allows scientists to…
CVE ID : CVE-2025-26186
Published : July 15, 2025, 5:15 p.m. | 9 hours, 44 minutes ago
Description : SQL Injection vulnerability in openSIS v.9.1 allows a remote attacker to execute arbitrary code via the id parameter in Ajax.php
Severity: 8.1 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-6558
Published : July 15, 2025, 6:15 p.m. | 8 hours, 44 minutes ago
Description : Insufficient validation of untrusted input in ANGLE and GPU in Google Chrome prior to 138.0.7204.157 allowed a remote attacker to potentially perform a sandbox escape via a crafted HTML page. (Chromium security severity: High)
Severity: 8.8 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-7656
Published : July 15, 2025, 6:15 p.m. | 8 hours, 44 minutes ago
Description : Integer overflow in V8 in Google Chrome prior to 138.0.7204.157 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page. (Chromium security severity: High)
Severity: 8.8 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-7657
Published : July 15, 2025, 6:15 p.m. | 8 hours, 44 minutes ago
Description : Use after free in WebRTC in Google Chrome prior to 138.0.7204.157 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page. (Chromium security severity: High)
Severity: 8.8 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-41236
Published : July 15, 2025, 7:15 p.m. | 7 hours, 44 minutes ago
Description : VMware ESXi, Workstation, and Fusion contain an integer-overflow vulnerability in the VMXNET3 virtual network adapter. A malicious actor with local administrative privileges on a virtual machine with VMXNET3 virtual network adapter may exploit this issue to execute code on the host. Non VMXNET3 virtual adapters are not affected by this issue.
Severity: 9.3 | CRITICAL
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-41237
Published : July 15, 2025, 7:15 p.m. | 7 hours, 44 minutes ago
Description : VMware ESXi, Workstation, and Fusion contain an integer-underflow in VMCI (Virtual Machine Communication Interface) that leads to an out-of-bounds write. A malicious actor with local administrative privileges on a virtual machine may exploit this issue to execute code as the virtual machine’s VMX process running on the host. On ESXi, the exploitation is contained within the VMX sandbox whereas, on Workstation and Fusion, this may lead to code execution on the machine where Workstation or Fusion is installed.
Severity: 9.3 | CRITICAL
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-41238
Published : July 15, 2025, 7:15 p.m. | 7 hours, 44 minutes ago
Description : VMware ESXi, Workstation, and Fusion contain a heap-overflow vulnerability in the PVSCSI (Paravirtualized SCSI) controller that leads to an out of-bounds write. A malicious actor with local administrative privileges on a virtual machine may exploit this issue to execute code as the virtual machine’s VMX process running on the host. On ESXi, the exploitation is contained within the VMX sandbox and exploitable only with configurations that are unsupported. On Workstation and Fusion, this may lead to code execution on the machine where Workstation or Fusion is installed.
Severity: 9.3 | CRITICAL
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-30743
Published : July 15, 2025, 8:15 p.m. | 6 hours, 44 minutes ago
Description : Vulnerability in the Oracle Lease and Finance Management product of Oracle E-Business Suite (component: Internal Operations). The supported version that is affected is 12.2.13. Easily exploitable vulnerability allows low privileged attacker with network access via HTTP to compromise Oracle Lease and Finance Management. Successful attacks of this vulnerability can result in unauthorized creation, deletion or modification access to critical data or all Oracle Lease and Finance Management accessible data as well as unauthorized access to critical data or complete access to all Oracle Lease and Finance Management accessible data. CVSS 3.1 Base Score 8.1 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:N).
Severity: 8.1 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-30744
Published : July 15, 2025, 8:15 p.m. | 6 hours, 44 minutes ago
Description : Vulnerability in the Oracle Mobile Field Service product of Oracle E-Business Suite (component: Multiplatform Sync Errors). Supported versions that are affected are 12.2.3-12.2.13. Easily exploitable vulnerability allows low privileged attacker with network access via HTTP to compromise Oracle Mobile Field Service. Successful attacks of this vulnerability can result in unauthorized creation, deletion or modification access to critical data or all Oracle Mobile Field Service accessible data as well as unauthorized access to critical data or complete access to all Oracle Mobile Field Service accessible data. CVSS 3.1 Base Score 8.1 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:N).
Severity: 8.1 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-30749
Published : July 15, 2025, 8:15 p.m. | 6 hours, 44 minutes ago
Description : Vulnerability in the Oracle Java SE, Oracle GraalVM for JDK, Oracle GraalVM Enterprise Edition product of Oracle Java SE (component: 2D). Supported versions that are affected are Oracle Java SE: 8u451, 8u451-perf, 11.0.27, 17.0.15, 21.0.7, 24.0.1; Oracle GraalVM for JDK: 17.0.15, 21.0.7 and 24.0.1; Oracle GraalVM Enterprise Edition: 21.3.14. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise Oracle Java SE, Oracle GraalVM for JDK, Oracle GraalVM Enterprise Edition. Successful attacks of this vulnerability can result in takeover of Oracle Java SE, Oracle GraalVM for JDK, Oracle GraalVM Enterprise Edition. Note: This vulnerability applies to Java deployments, typically in clients running sandboxed Java Web Start applications or sandboxed Java applets, that load and run untrusted code (e.g., code that comes from the internet) and rely on the Java sandbox for security. This vulnerability does not apply to Java deployments, typically in servers, that load and run only trusted code (e.g., code installed by an administrator). CVSS 3.1 Base Score 8.1 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H).
Severity: 8.1 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…
CVE ID : CVE-2025-30751
Published : July 15, 2025, 8:15 p.m. | 6 hours, 44 minutes ago
Description : Vulnerability in the Oracle Database component of Oracle Database Server. Supported versions that are affected are 19.3-19.27 and 23.4-23.8. Easily exploitable vulnerability allows low privileged attacker having Create Session, Create Procedure privilege with network access via Oracle Net to compromise Oracle Database. Successful attacks of this vulnerability can result in takeover of Oracle Database. CVSS 3.1 Base Score 8.8 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H).
Severity: 8.8 | HIGH
Visit the link for more details, such as CVSS details, affected products, timeline, and more…