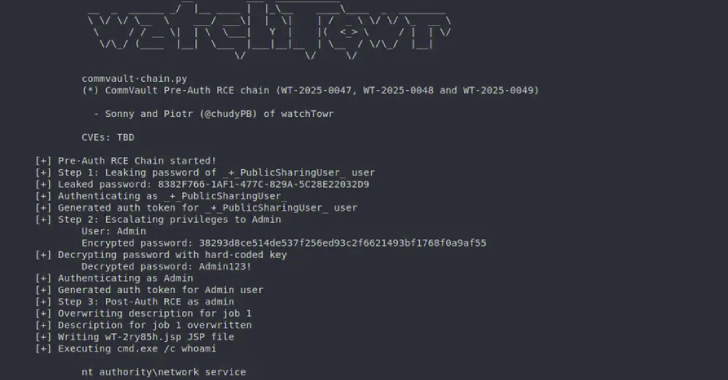
Commvault has released updates to address four security gaps that could be exploited to achieve remote code execution on susceptible instances.
The list of vulnerabilities, identified in Commvault versions before 11.36.60, is as follows –
CVE-2025-57788 (CVSS score: 6.9) – A vulnerability in a known login mechanism allows unauthenticated attackers to execute API calls without requiring user
Source: Read More