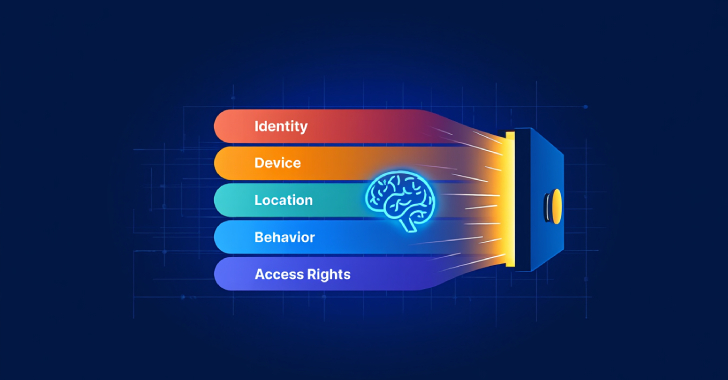
By 2025, Zero Trust has evolved from a conceptual framework into an essential pillar of modern security. No longer merely theoretical, it’s now a requirement that organizations must adopt. A robust, defensible architecture built on Zero Trust principles does more than satisfy baseline regulatory mandates. It underpins cyber resilience, secures third-party partnerships, and ensures uninterrupted
Source: Read More
![How to focus on building your skills when everything’s so distracting with Ania Kubów [Podcast #187]](https://devstacktips.com/wp-content/uploads/2025/09/f7c52449-77f9-4fa4-bbd5-34c3773658dd-6kiwIT-450x253.png)