Previously we have talked a lot of phishing tools like Zphisher, LockPhish, SocialPhish, Weeman etc. They are getting outdated so, today we are going to learn about AdvPhishing. AdvPhishing is an advanced phishing toolkit that bad guys use to gain access to victim’s social media account.
But in our this article we learn about it’s work and how we can be safe from it’s attacks. Let’s talk about how we can use this tool on our Linux system.
Installing AdvPhishing
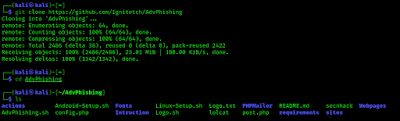
We need to clone AdvPhishing from it’s GitHub repository by using the following command on our terminal:
git clone https://github.com/Ignitetch/AdvPhishingThen it will start cloning the repository. After completing the cloning we can navigate to it’s directory by using following cd command:
cd AdvPhishingNow we can setup permissions and run the installer for Linux by using following command:
sudo chmod +x Linux-Setup.sh && sudo bash Linux-Setup.sh<br />This will download some additional requirements to run the tool. This will ask our root password and may take some time depending on our internet speed and system performance. If we are in Android device using Termux, then we need to run following command:
chmod +x Android-Setup.sh && bash Android-Setup.sh<br />Then it will ask about our ngrok token as we can see in the following screenshot:
Here we need to put our ngrok API token. But how to get it? To get ngrok API token we need to sign up on ngrok’s official page from our browser. There we need to fill up some information as we can see in the following screenshot:
 |
| Pro Tip:- During this we can use Disposable mail ids |
After signing up we can see our authentication token on this page, we can see it on the following screenshot:
We need to put this on our terminal as we did in the following screenshot:
 |
| Pro Tip:- To paste clipboard on Linux terminal we can use Ctrl+Shift+V |
Then we need to hit enter to Installed it successfully. Now we can run it by applying following command:
./AdvPhishing.sh<br />Then it will ask that we are using this for educational purpose or not. We are using it for educational purpose only so we press y and hit enter. After this main screen of AdvPhishing will comes in front of us as following screenshot:
Here it has listed lot of website we can choose anything from this menu and enter the number. For an example we choose Facebook and it’s number is 2. So we press 2 and hit Enter.
Then it will start PHP server and ngrok server then ask us if we want to modify the URL or not?
We hit “Y” then it will ask us some social engineering keywords, as we can see in the following screenshot:
Source: Read More