Researchers from the U.S. National Institute of Standards and Technology (NIST) and the Cybersecurity and Infrastructure Security Agency (CISA) have developed a new security metric to determine the likelihood that a vulnerability has been exploited.
In a paper published this week, Peter Mell, formerly of NIST, and CISA’s Jonathan Spring outlined their vulnerability exploit metric that augments the work of the Exploit Prediction Scoring System (EPSS) and CISA’s Known Exploited Vulnerabilities (KEV) catalog.
Mell and Spring cited studies that have found that only 5% of vulnerabilities have been observed to be exploited in the wild, while the monthly vulnerability remediation rate for companies is 16%.
“The remediation rate is so low because it is expensive for companies to address vulnerabilities,” they wrote. “…This situation would not be a problem if the 16% were to cover the 5%, but metrology is lacking to accurately make that calculation. Thus, predicting which vulnerabilities will be exploited is critically important for the efficiency and cost-effectiveness of enterprise vulnerability remediation efforts.”
Vulnerability Exploit Metric Builds on EPSS
Mell and Spring noted known shortcomings in EPSS and the CISA KEV catalog.
EPSS “has known inaccurate values,” they wrote, while KEV is likely not comprehensive. Their proposed likelihood metric could help augment EPSS remediation by correcting some inaccuracies, and could build on the KEV catalog by “enabling measurements of comprehensiveness.”
EPSS provides probabilities that a vulnerability will be observed to be exploited in the wild within the next 30 days, the NIST and CISA researchers said. “However, its probabilities are known to be inaccurate for vulnerabilities that have been previously observed to be exploited,” they wrote. “… Fortunately, the probabilities are not randomly inaccurate; they underestimate the true probability.”
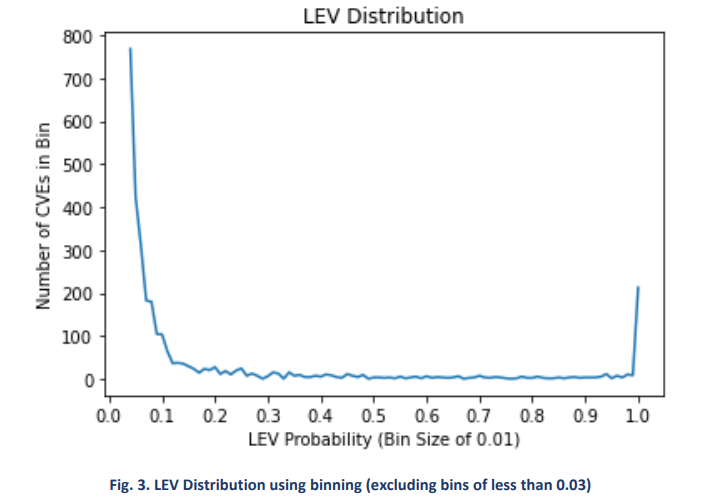
Mell and Spring call their formula Likely Exploited Vulnerabilities (LEV) probabilities. LEV probabilities have at least four use cases, they said. These include:
- Measuring the expected number and proportion of vulnerabilities that actors have exploited
- Estimating the comprehensiveness of the KEV catalog
- Augmenting KEV-based vulnerability remediation prioritization by “identifying higher probability vulnerabilities that may be missing”
- Augmenting EPSS-based vulnerability remediation prioritization by “identifying vulnerabilities that may be underscored.”
Results: Hundreds of Vulnerabilities with High Probability of Exploitation
The paper listed two vulnerabilities where LEV and EPSS probabilities differed.
For CVE-2023-1730, a SQL injection vulnerability in the SupportCandy WordPress plugin before 3.1.5, the LEV probability was 0.70, while the peak EPSS score was 0.16.
For CVE-2023-29373, a Microsoft ODBC Driver Remote Code Execution vulnerability, the LEV probability was 0.54350, while the peak EPSS probability was 0.08.
Their work also identified several hundred vulnerabilities with a probability approaching 1.0.
“Interestingly, many of these vulnerabilities are not included in tested KEV lists,” Mell and Spring wrote. “… This is one reason that LEV lists cannot replace KEV lists. LEV cannot identify which of the many low probability vulnerabilities will be exploited, it can only help compute how many of them are expected to be exploited. KEV lists identify the exact ones that have been exploited.”
Mell and Spring said they’re looking for industry partners to collaborate with to obtain performance measurements of the LEV metric.
Source: Read More