Threat actors have been observed distributing malicious payloads such as cryptocurrency miner and clipper malware via SourceForge, a popular software hosting service, under the guise of cracked versions of legitimate applications like Microsoft Office.
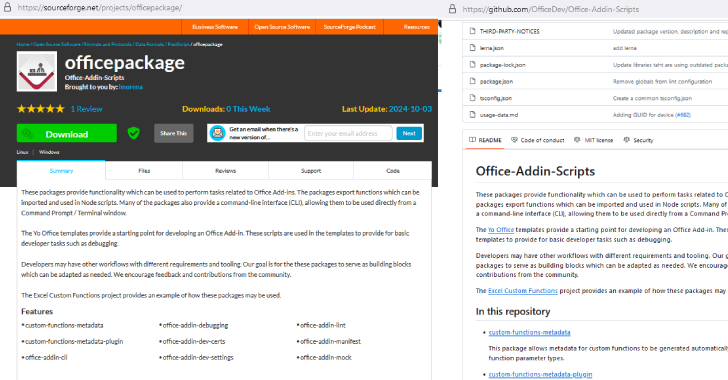
“One such project, officepackage, on the main website sourceforge.net, appears harmless enough, containing Microsoft Office add-ins copied from a
Source: Read More