Exploring new frontiers in cybersecurity is essential as digital threats evolve. Traditional approaches, such as manual source code audits and reverse engineering, have been foundational in identifying vulnerabilities. Yet, the surge in the capabilities of Large Language Models (LLMs) presents a unique opportunity to transcend these conventional methods, potentially uncovering and mitigating previously undetectable security vulnerabilities.
The challenge in cybersecurity is the persistent threat of ‘unfuzzable’ vulnerabilities—flaws that evade detection by conventional automated systems. These vulnerabilities represent significant risks, as they often go unnoticed until exploited. The advent of sophisticated LLMs offers a promising solution by potentially replicating the analytical prowess of human experts in identifying these elusive threats.
Over the years, the research team at Google Project Zero has synthesized insights from their extensive experience in human-powered vulnerability research to refine the application of LLMs in this field. They identified key principles that harness the strengths of LLMs while addressing their limitations. Crucial to their findings is the importance of extensive reasoning processes, which have proven effective across various tasks. An interactive environment is essential, allowing models to adjust and correct errors dynamically, enhancing their effectiveness. Furthermore, equipping LLMs with specialized tools, such as debuggers and Python interpreters, is vital for mimicking human researchers’ operational environment and conducting precise calculations and state inspections. The team also emphasizes the need for a sampling strategy that allows the exploration of multiple hypotheses through distinct trajectories, facilitating more comprehensive and effective vulnerability research. These principles leverage LLMs’ capabilities for more accurate and reliable outcomes in security tasks.
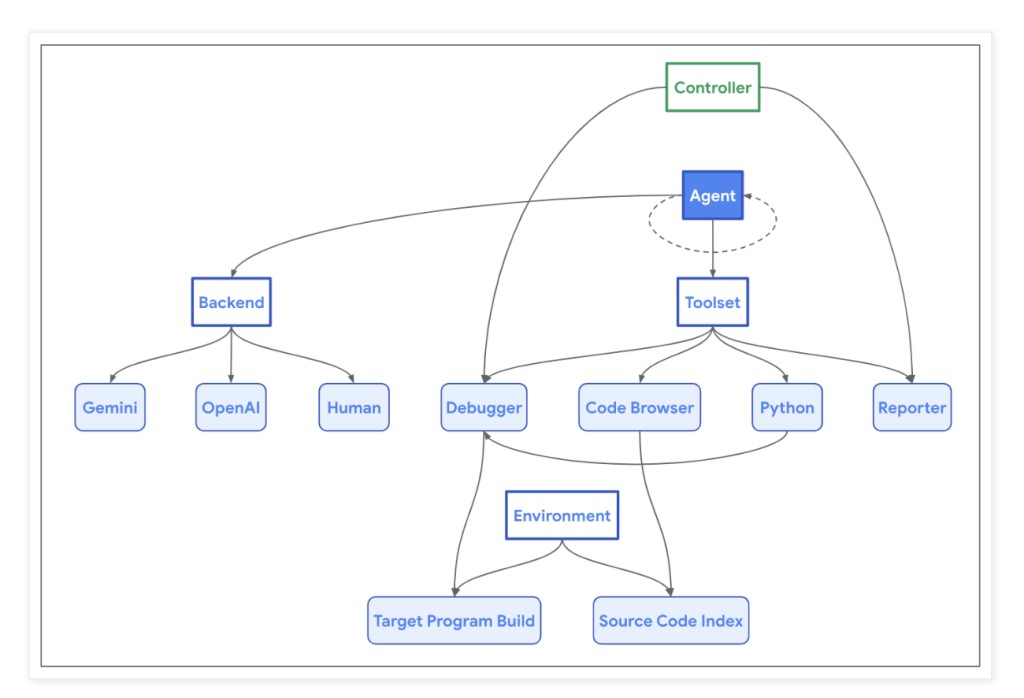
The research team has developed “Naptime,†a pioneering architecture for LLM-assisted vulnerability research. Naptime incorporates a specialized architecture that equips LLMs with specific tools to enhance their ability to perform security analyses effectively. A key aspect of this architecture is its focus on grounding through tool usage, ensuring that the LLMs’ interactions with the target codebase closely mimic the workflows of human security researchers. This approach allows for automatic verification of the agent’s outputs, a vital feature considering the autonomous nature of the system.
The Naptime architecture centers on the interaction between an AI agent and a target codebase, equipped with tools like the Code Browser, Python tool, Debugger, and Reporter. The Code Browser allows the agent to navigate and analyze the codebase in-depth, similar to how engineers use tools like Chromium Code Search. The Python tool and Debugger enable the agent to perform intermediate calculations and dynamic analyses, enhancing the precision and depth of security testing. These tools work together within a structured environment to detect and verify security vulnerabilities autonomously, ensuring the integrity and reproducibility of the research findings.
Researchers have integrated the Naptime architecture with CyberSecEval 2 evaluation, substantially improving LLM security test performance. For “Buffer Overflow†scenarios, GPT 4 Turbo’s scores surged to perfect passes using the Naptime architecture, achieving 1.00 across multiple trials, compared to its initial scores of 0.05. Similarly, enhancements were evident in the “Advanced Memory Corruption†category, with GPT 4 Turbo’s performance increasing from 0.16 to 0.76 in more complex test scenarios. The Gemini models also showed marked improvements; for instance, Gemini 1.5 Pro’s scores in Naptime configurations rose to 0.58, demonstrating significant advancements in handling complex tasks compared to the initial testing phases. These results underscore the efficacy of the Naptime framework in enhancing the precision and capability of LLMs in conducting detailed and accurate vulnerability assessments.
To conclude, the Naptime project demonstrates that LLMs can significantly enhance their performance in vulnerability research with the right tools, particularly in controlled testing environments such as CTF-style challenges. However, the true challenge lies in translating this capability to the complexities of autonomous offensive security research, where understanding system states and attacker control is crucial. The study underscores the need to provide LLMs with flexible, iterative processes akin to those employed by expert human researchers to reflect their potential truly. As the team at Google Project Zero, in collaboration with Google DeepMind, continues to develop this technology, they remain committed to pushing the boundaries of what LLMs can achieve in cybersecurity, promising more sophisticated advancements in the future.
The post Google Project Zero Introduces Naptime: An Architecture for Evaluating Offensive Security Capabilities of Large Language Models appeared first on MarkTechPost.
Source: Read MoreÂ