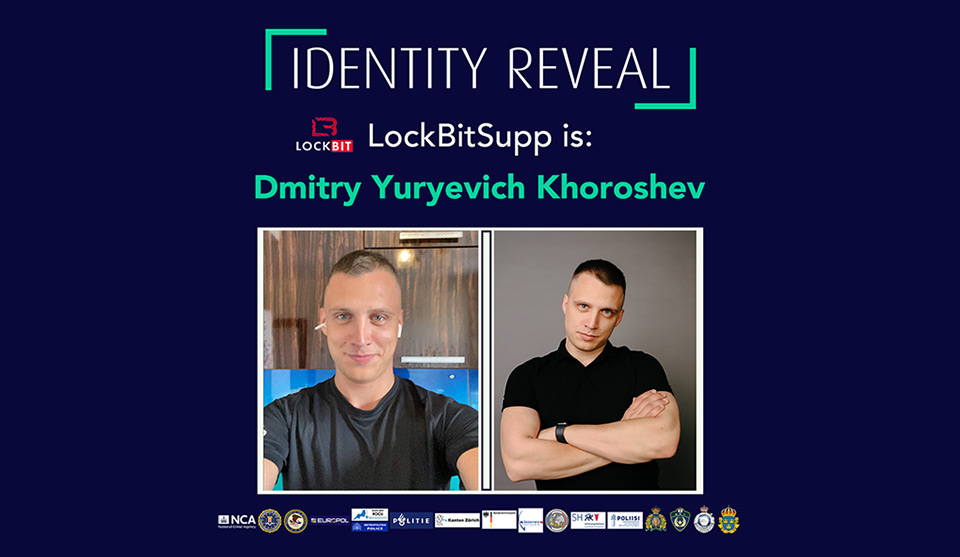
In a landmark international operation, Dmitry Khoroshev, the once-anonymous leader behind the notorious LockBit Ransomware gang has been unmasked and heavily sanctioned. The announcement was made simultaneously today by the UK’s Foreign, Commonwealth and Development Office (FCDO), the US Department of the Treasury’s Office of Foreign Assets Control (OFAC), and the Australian Department of Foreign Affairs. The coordinated effort involved the UK, US, and Australia, marking a significant victory in the battle against cybercrime.
Khoroshev, also known as LockBitSupp, who famously offered a $10 million reward for anyone who could expose his identity, is now facing asset freezes and travel bans. This decisive action was announced by the UK’s Foreign, Commonwealth & Development Office, the US Department of the Treasury’s Office of Foreign Assets Control, and the Australian Department of Foreign Affairs.
LockBit Leader Unmasked
The unveiling of Khoroshev’s identity is part of an extensive crackdown by the Operation Cronos taskforce, which includes the NCA, FBI, and other global partners. This follows a series of operations which saw the infiltration and disruption of LockBit’s network. The cyber group, known for its ransomware-as-a-service model, has significantly weakened, operating at a reduced capacity due to the relentless international efforts.
This groundbreaking operation has not only demystified one of the cyber world’s most elusive figures but also inflicted a severe blow to the LockBit group’s operations, signaling a impactful global stance against cyber threats and ransomware criminals.
LockBit’s Downfall: Disruption Leads to Reduction in Global Threats
In February, authorities announced a significant breach in LockBit’s defenses, gaining control over their dark web leak site and severely compromising the group’s operational capabilities. The severity of LockBit’s criminal activities was fully unveiled through this intervention, revealing that from June 2022 to February 2024, the group had orchestrated over 7,000 ransomware attacks globally, impacting major sectors including healthcare. The most affected regions included the United States, United Kingdom, France, Germany, and China.
The data obtained from LockBit’s systems indicated that the attacks targeted more than 100 hospitals and healthcare entities, pushing at least 2,110 victims into negotiation with the cybercriminals. Despite their attempts to regroup and revive their operations, LockBit’s capabilities remain stifled, running at a limited capacity with a considerably reduced global threat.
Interestingly, in their desperation to appear active, LockBit created a new leak site post-disruption, inflating their activity by claiming older attacks and those conducted by other ransomware groups. However, the effectiveness of their operations has significantly dwindled, as indicated by a 73% decrease in the average monthly attacks in the UK post-February 2024, with similar reductions reported worldwide.
The identification of Dmitry Khoroshev has provided invaluable insights into LockBit’s inner workings, exposing the real-world implications of their actions. Of the 194 affiliates identified as part of LockBit’s network until February 2024, 148 were involved in building attacks, and 119 engaged in negotiations with victims.
Disturbingly, 114 of these affiliates paid substantial sums to join LockBit’s programs but failed to make any money from their criminal activities, highlighting the deceptive and exploitative nature of LockBit’s operations.
Moreover, the NCA’s investigation revealed numerous instances where LockBit’s decryptor tools failed to function correctly, leaving victims who had paid ransoms without any solution and no support from the group’s affiliates. One particularly egregious incident involved an attack on a children’s hospital in December 2022, where LockBitSupp issued a statement apologizing and provided a free decryptor, claiming the affiliate had violated their rules and was expelled from the program.
However, NCA analysis showed that the affiliate remained active and continued to conduct 127 unique attacks, engage in 50 negotiations, and received multiple ransom payments until the group’s disruption in February 2024.
NCA Director General Graeme Biggar emphasized the operation’s success, stating, “These sanctions are hugely significant and show that there is no hiding place for cyber criminals like Dmitry Khoroshev, who wreak havoc across the globe. He was certain he could remain anonymous, but he was wrong.
Biggar added, “We know our work to disrupt LockBit thus far has been extremely successful in degrading their capability and credibility among the criminal community. The group’s attempt at rebuilding has resulted in a much less sophisticated enterprise with significantly reduced impact.â€
Sanctions Minister Anne-Marie Trevelyan also highlighted the collaborative nature of this international effort, noting, “Together with our allies we will continue to crack down on hostile cyber activity which is destroying livelihoods and businesses across the world. In sanctioning one of the leaders of LockBit we are taking direct action against those who continue to threaten global security, while simultaneously exposing the malicious cyber-criminal activity emanating from Russia.â€
As part of the ongoing efforts to mitigate the damage caused by LockBit, the NCA and its partners have gained possession of over 2,500 decryption keys and are actively reaching out to nearly 240 victims in the UK, offering support and recovery solutions. The public is encouraged to report any cyber incidents immediately through the government’s Cyber Incident Signposting Site, which directs users to the appropriate agencies for further action.
The Operation Cronos taskforce continues to operate at full capacity, involving a wide array of international law enforcement agencies from the US, UK, EU, and beyond, demonstrating a unified front against cyber threats. This coalition serves as a stark reminder that the international community remains vigilant and ready to employ all available resources to combat cybercrime and protect global security.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.
Source: Read More