Objective: Enable resource monitoring for AWS EC2 instances using the Dynatrace monitoring tool (OneAgent) to gain real-time insights into system performance, detect anomalies, and optimize resource utilization.
What is Dynatrace?
Dynatrace is a platform for observability and application performance monitoring (APM) that delivers real-time insights into application performance, infrastructure oversight, and analytics powered by AI. It assists teams in detecting, diagnosing, and resolving problems more quickly by providing comprehensive monitoring across logs, metrics, traces, and insights into user experience.
Dynatrace OneAgent
Dynatrace OneAgent is primarily a single binary file that comprises a collection of specialized services tailored to your monitoring setup. These services collect metrics related to various components of your hosts, including hardware specifications, operating systems, and application processes. The agent also has the capability to closely monitor specific technologies (such as Java, Node.js, and .NET) by embedding itself within these processes and analyzing them from the inside. This enables you to obtain code-level visibility into the services that your application depends on.
Key Features of Dynatrace OneAgent
- Automatic Deployment – OneAgent installs automatically and starts collecting data without manual configuration.
- Full-Stack Monitoring – It monitors everything from application code to databases, servers, containers, and networks.
- AI-Powered Insights – Works with Dynatrace’s Davis AI engine to detect anomalies and provide root cause analysis.
- Auto-Discovery – Automatically detects services, processes, and dependencies.
- Low Overhead – Designed to have minimal impact on system performance.
- Multi-Platform Support – Works with Windows, Linux, Kubernetes, AWS, Azure, GCP, and more.
Prerequisites to Implement OneAgent
- Dynatrace account
- AWS EC2 instance with Linux as the operating system and enable the SSH port (22).
How to Implement Dynatrace OneAgent
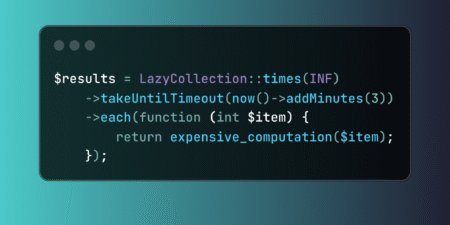
Step 1. Dynatrace OneAgent configuration
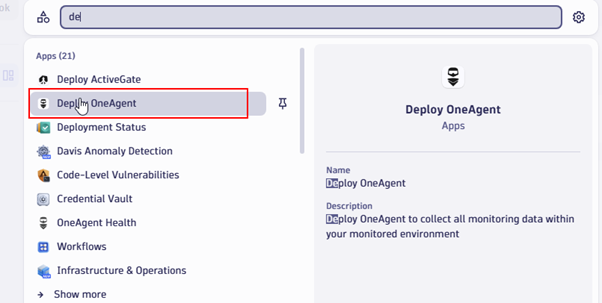
Log in to the Dynatrace portal and search for Deploy OneAgent.
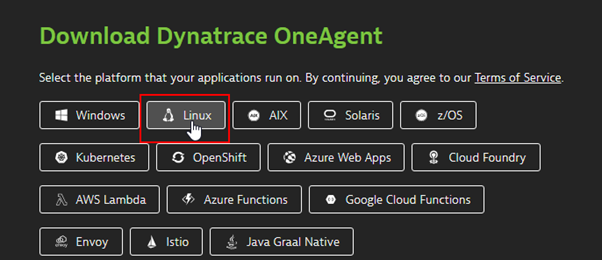
Select the platform on which your application is running. In our case, it is Linux.
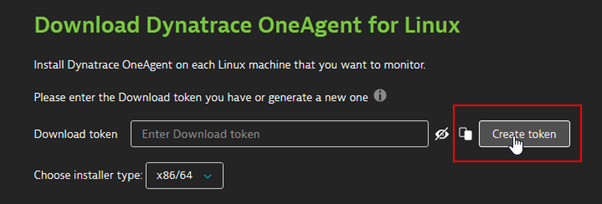
Create a token that is required for authentication.
After generating a token, you will receive a command to download and execute the installer on the EC2 instance.
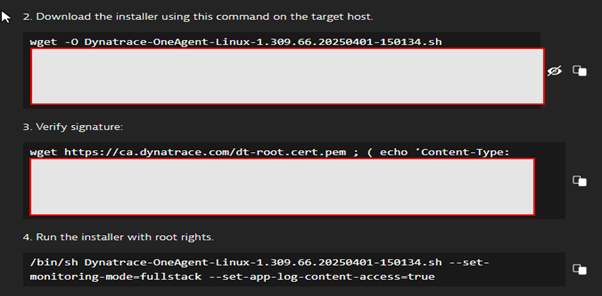
Step 2: Log in to the EC2 instance using SSH and run the command to download the installer.
After this, run the command to run the installer.

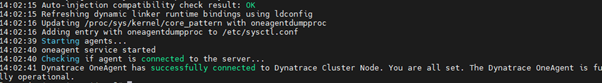
The Dynatrace one agent has now been installed on the EC2 instance.
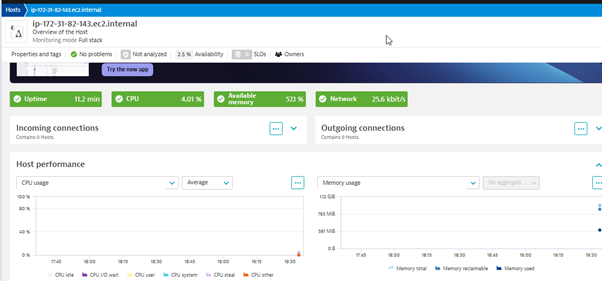
Output
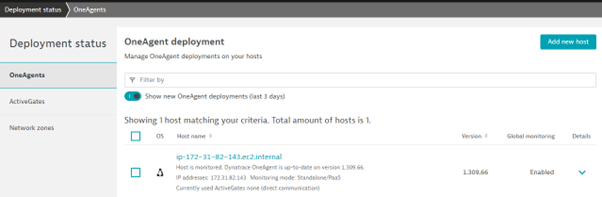
Now we can monitor various resource usage based on application and infrastructure level on the Dynatrace dashboard.
Conclusion
Enabling resource monitoring for AWS EC2 instances using Dynatrace provides comprehensive observability, allowing teams to detect performance issues, optimize resource utilization, and ensure application reliability. By leveraging Dynatrace OneAgent, organizations can automate monitoring, gain AI-driven insights, and enhance cloud efficiency. Implementing this solution not only improves operational visibility but also facilitates proactive troubleshooting, reduces downtime, and optimizes cloud costs.
Source: Read MoreÂ